Topic: * - on January 3, 2024 at 6:53:00 PM CET
Ganja Chicken aus Thailand
Cannabisfutter statt Antibiotika verbessert die Gesundheit von Hühnern In einer neuen Studie haben Forscher der Universität Chiang Mai in Thailand herausgefunden, dass Cannabisfutter die Gesundheit und Fleischqualität von Hühnern verbessern kann. Die Studie, die sich aktuell noch in der Peer-Review befindet, untersuchte die Auswirkungen der Verwendung von Marihuanablättern als Futterzusatz für Masthühner und kommt zu erstaunlichen Ergebnissen.
... Link (0 comments) ... Comment
Topic: * - on January 3, 2024 at 5:42:00 PM CET
Forscher sammeln Darmbakterien aus aller Welt
Ein Kühlschrank voller Kot, das ist der Grundstein für ein ehrgeiziges Projekt: Schweizer Wissenschaftlerinnen und Wissenschaftler wollen einen Tresor für Darmbakterien aus aller Welt anlegen – und damit die bedrohte Artenvielfalt im Darm retten.

orf.at . . . spektrum.de
... Link (0 comments) ... Comment
Topic: * - on January 3, 2024 at 5:34:00 PM CET
Menschen erkennen zufriedenes Gackern
Wenn Hühner Futter erhalten, gackern sie anders als etwa bei Bedrohung. Eine aktuelle Studie zeigt, dass ein Großteil der Menschen die „Hühnersprache“ versteht – also erkennt, welche Gefühle hinter eine Lautäußerung stecken. Das ließe sich für bessere Haltungsbedingungen nutzen.
... Link (0 comments) ... Comment
Topic: * - on December 21, 2023 at 3:25:00 PM CET
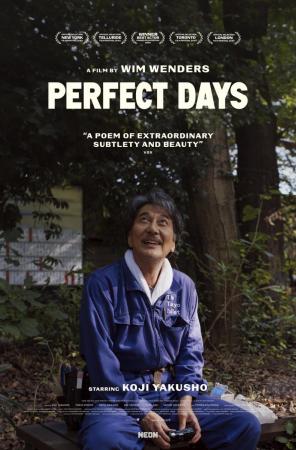
Perfect Days - Wim Wenders’ neuer Film feiert japanische Toiletten
Er arbeitet als Reinigungskraft in öffentlichen Toiletten. Er putzt sehr gewissenhaft. Die Handgriffe sind einstudiert, der Ablauf bleibt sich gleich. Der Mann bückt sich mit schnellen Bewegungen nach dem Abfall, den die Leuten liegen gelassen haben, er sammelt Fitzelchen ein, leere WC-Papier-Rollen. Dann zieht er sich die Gummihandschuhe über. Er macht die Kloschüssel sauber. Er seift das Sieb im Urinal ein. Mit einem kleinen Kontrollspiegel inspiziert er die Unterseite der WC-Sitz-Erhöhung. Anschliessend poliert er die Armaturen. Nimmt mit einem Wischmopp den Boden auf. Ein Mann macht seinen Job, er macht ihn gut – und er wirkt zufrieden dabei.
Hirayama, so heisst er, arbeitet für «The Tokyo Toilet», das steht auf seinem Overall. Wim Wenders’ neuer, in Japan realisierter Kinofilm «Perfect Days» dreht sich um ihn: einen glücklichen Toilettenreiniger in der Hauptstadt.
... Link (0 comments) ... Comment
Topic: AUSTRIA - on December 11, 2023 at 4:13:00 PM CET
Österreichische Strohmänner
... Link (0 comments) ... Comment
Topic: BOARD NEWS - on December 8, 2023 at 8:17:00 PM CET
VR-Brille für Mäuse entwickelt
Mäuse gehören zu den wichtigsten Labortieren der Wissenschaft. Um sie noch genauer untersuchen zu können, entwickelten Fachleute nun ein besonderes Werkzeug: eine Brille, die ähnlich wie bei Menschen virtuelle Realitäten (VR) erzeugt.
... Link (1 comment) ... Comment
Topic: BOARD NEWS - on December 8, 2023 at 8:14:00 PM CET
Wasser vor dem Mahlen macht Kaffee aromatischer
Sogar die erfahrensten Baristas schaffen es nicht, aus denselben Bohnen immer gleich guten Kaffee zu brühen. Wie eine aktuelle Studie zeigt, helfen ein paar Spritzer Wasser vor dem Mahlen. Die Feuchtigkeit macht den Mahlvorgang nicht nur effizienter, sie verhindert auch Klumpen. Das verbessert das Aroma und sorgt für gleichbleibende Qualität.
... Link (0 comments) ... Comment
Topic: BOARD NEWS - on December 7, 2023 at 4:57:00 AM CET
La grande bataille des toilettes
Poop hat einen schlechten Ruf. Es ist das Tabu, das wir so schnell wie möglich loswerden wollen, der ultimative Abfall, den wir gerne geruchlos und unsichtbar haben möchten. Es steht jedoch im Mittelpunkt eines globalen Wirtschaftskampfes und einer technologischen und kulturellen Revolution, deren Epizentren Genf und die Schweiz sind. Weltweit erleben Toiletten eine Revolution wie keine andere seit dem 19. Jahrhundert. Bill Gates investiert Hunderte Millionen Dollar in die Entwicklung neuer Arten von Sanitäranlagen. Indien installiert Millionen von Latrinen, damit niemand seine Notdurft im Freien verrichtet.
Diese Live-Übertragung beginnt am Sonntag, 10. Dezember 2023, um 2:40 Uhr
... Link (0 comments) ... Comment
Topic: BOARD NEWS - on November 6, 2023 at 10:52:00 PM CET
Wiens WCs unter den dreckigsten in Europa
Wiens öffentliche Toiletten sind laut einer auf Google-Rezensionen basierenden Auswertung des britischen Sanitärhändlers Showers to you europaweit unter den schmutzigsten. Sie belegen den sechsten Platz im Ranking.
... Link (0 comments) ... Comment
Topic: BOARD NEWS - on October 19, 2023 at 8:53:00 AM CEST
Toter Hahn krähte in Kühlkammer plötzlich wieder
Eine kuriose Geschichte sorgt in Roggendorf (Bezirk Melk) für Gesprächsstoff. Ein toter Hahn wurde, nachdem er bei der Tierkörpersammelstelle abgegeben worden war, nach einer Nacht lebendig in der Kühlkammer wiedergefunden.
... Link (1 comment) ... Comment
Topic: KAMELE - on October 16, 2023 at 1:25:00 PM CEST
Kamele nahmen in Hallein Reißaus
Am Montag in den frühen Morgenstunden haben im Stadtgebiet von Hallein (Tennengau) acht Kamele Reißaus genommen. Die Tiere gingen von einem Zirkusgelände in Richtung Bahnhof. Grund dürfte ein Stromausfall gewesen sein.
... Link (0 comments) ... Comment
Topic: BOARD NEWS - on October 8, 2023 at 10:50:00 PM CEST
Hornochse
... Link (0 comments) ... Comment